Supply chain risk management made easy
Identify risks across your supply chain with automated scans, data lookups and digital questionnaires. Made in EU.










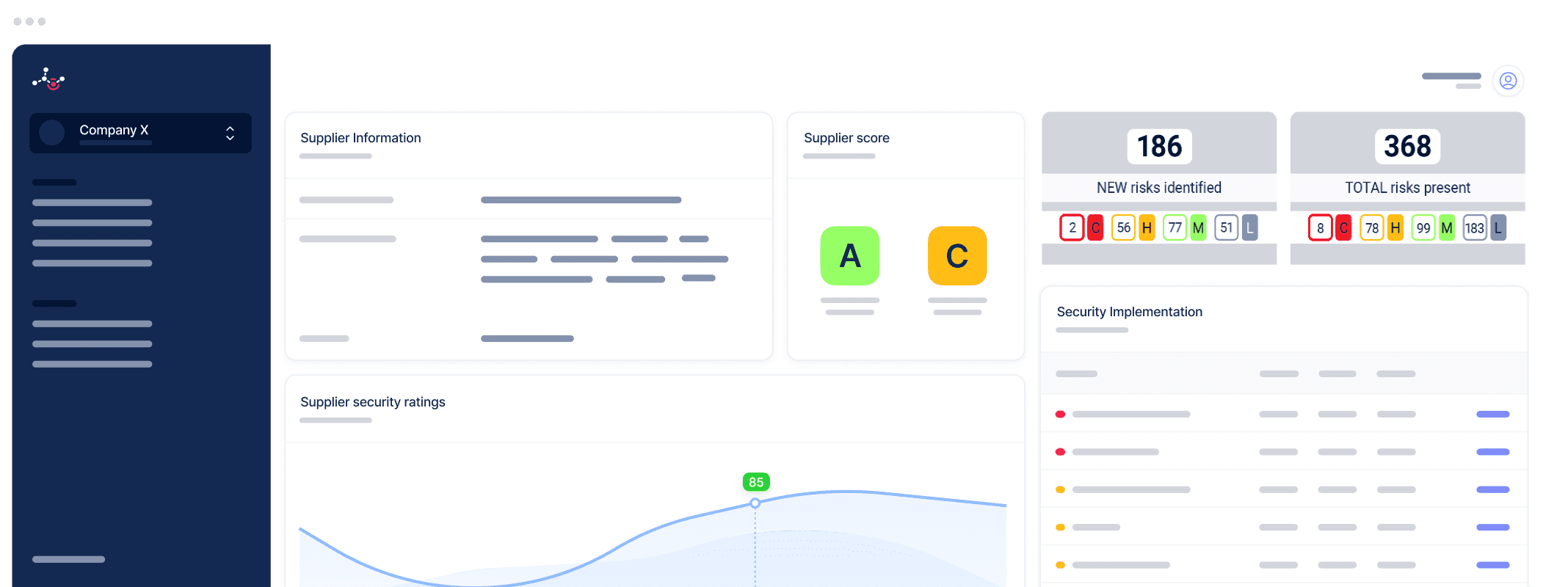
Comprehensive third-party risk assessment across all domains
Digital questionnaires are a flexible tool to assess a wide range of risks—cybersecurity, financial, ESG, compliance, and more. However, their results are often subjective and difficult to verify.
Ceeyu combines digital questionnaires with automated attack surface scans and data lookups to provide objective, real-time insights into your critical suppliers' risks. This dual approach ensures a more accurate, actionable, and holistic view of third-party risk management (TPRM).
Suppliers also have access to their results, empowering them to address issues proactively, no matter the risk domain.
+6.000.000 risks identified in customer supply chains
A
Average rating measured in the
Financial sector
C
Average rating measured in the
Pharmaceutical sector
D
Average rating measured in the
Manufacturing
Ceeyu TPRM SaaS Features
A powerful Software-as-a-Service risk identification and management platform that puts you in control of third-party risks.
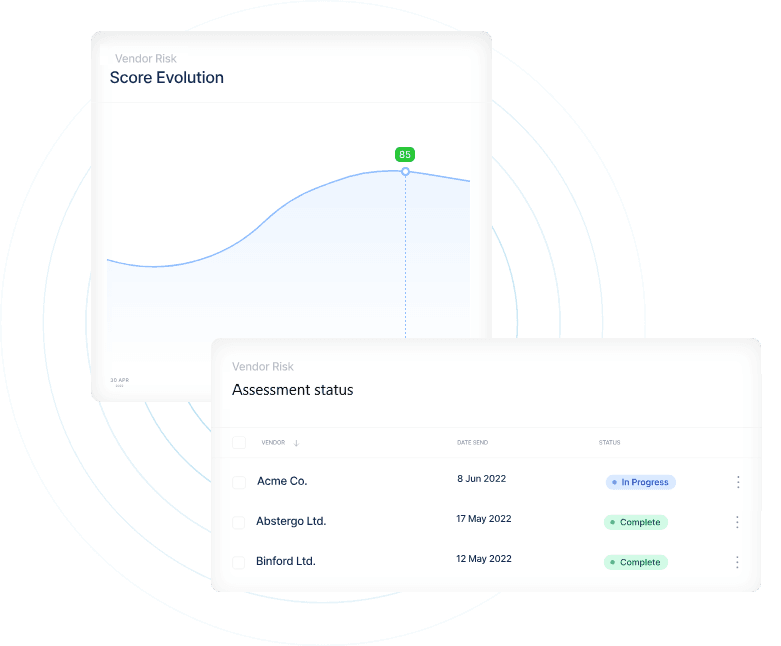
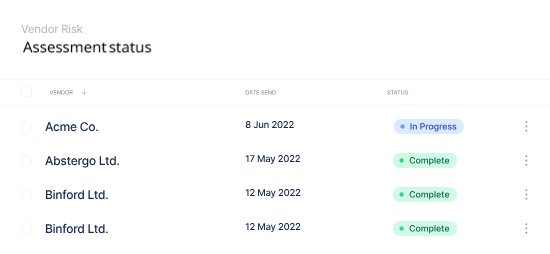
Digital questionnaires
Easily identify risks with a powerful digital questionnaire platform featuring built-in project management.
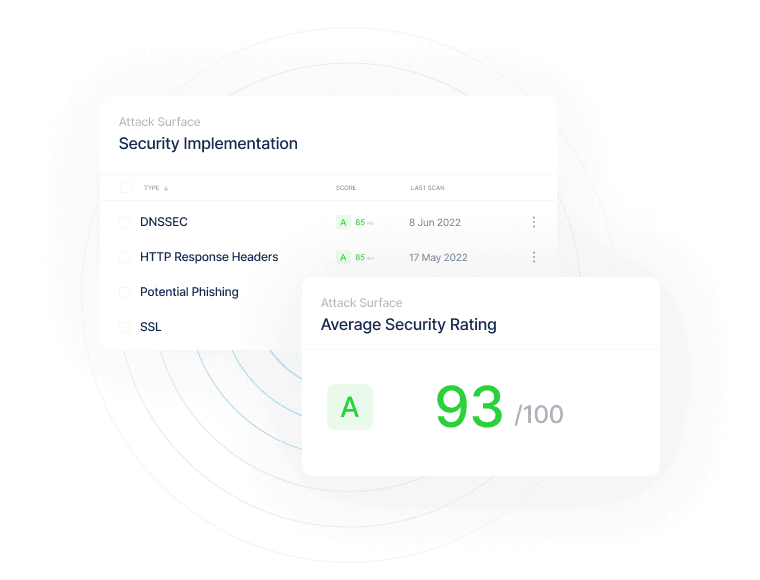
Attack surface management (ASM)
Visualize security posture of vendors, continuously scan for vulnerabilities and mitigate security risks, as required by NIS2.
Digital Footprint Monitoring
Uncover your forgotten IT systems, unauthorized use of cloud services, unlawful publication of URLs or email addresses.
Risk ratings
Understand risks and manage priorities thanks to a customizable risk severity scoring system.
Professional services
Outsource your third-party risk management administration, focus on risk management.
Why Ceeyu
Digital third-party risk management, complemented by automated security scans, in a user-friendly SaaS platform
Identify and manage cyber threats like ransomware, phishing, and cloud breaches, along with operational and third-party supply chain risks, using Ceeyu’s all-in-one risk assessment and management platform.
Identify and manage risks of any kind (data privacy, cybersecurity, regulatory, ESG,...)
Understand the attack surface of your company, and your supply chain
Actionable risk ratings
EU-based company & platform, data protected by EU law
Collaborate with suppliers to resolve risks
Customize to incorporate your own risk and procurement policies
Contributes to compliance with regulations like NIS2 and DORA, and frameworks like ISO 27001
Ceeyu features
EU made
Automated security scans
Not just security
Intuitive & collaborative
SaaS pricing
Assess the risks of your key suppliers and interact with them to remedy these.
An incident at one of your critical suppliers can disrupt your operations and impact business continuity. Ceeyu’s TPRM platform helps you proactively identify and mitigate supply chain risks through digital questionnaires, external data lookups, and advanced external attack surface monitoring (EASM).
Assess and manage vendor risk across multiple domains — including cybersecurity, compliance, financial health, and even 4th party risks — on a single, easy-to-use SaaS platform.
Ensure business continuity
Comply with NIS2 and DORA
Get your ISO 27001, CIS or NIST certification
Third-party risk management, without the hassle
"Based on the risks identified by Ceeyu's SaaS platform, we can focus our resources on strengthening the security of our digital footprint and supply chain where needed."
Ruben Annemans
Head of Security at GlobalSign

"Using Ceeyu we can identify and respond to risks in our supply chain and attack surface quickly, accurately and efficiently."
Jeroen Roelandt
CISO

"Ceeyu's SaaS platform automates many of the cumbersome processes that characterize TPRM, allowing us to reduce the time spent for our customers on this activity by 50%.”
Nick Prescot
Director CISO services

“We chose to work with Ceeyu because it has the right feature set for risk assessments, nothing more and nothing less. This makes it far more efficient than other platforms that are full of features but difficult to work with.”
Christophe Rome
CISO

“Ceeyu has improved the way we manage supply chain risk as part of our ISO 27001 requirements. Its affordable platform is far more efficient than juggling Excel files and emails. With Ceeyu, we streamline our assessments and get clear visibility of our supplier risks, making ISO compliance and security management easier than ever before.”
Genkis Gurlek
ICT & Procurement manager

Ready to get started?
Book a call with our cybersecurity experts, or try it yourself, free of charge!