
Many medium to large companies have obtained ISO 27001 certification. The question on most corporate management's minds: is the certificate sufficient to meet the NIS2 requirements?
CEEYU BLOGPOST
NIS2 Compliance
The NIS (Network and Information Systems) regulation aims to combat threats to networks and information systems, thereby improving the functioning of Europe's digital economy. Networks and information systems play a vital role in society as a whole, and their reliability and security are essential to economic and social activities. By October 2024, member states must transpose the NIS 2 regulation into their national legislation, which means that from that date onwards, companies in a sector considered essential or important to society will have to meet a number of requirements for the protection of their networks and information systems.
But NIS 2 is not just about regulatory compliance. It's about doing business successfully in the future, ensuring business continuity, preventing a cybersecurity attack and minimizing its consequences should it occur.

CEEYU BLOGPOST
NIS2 applies to medium and large enterprises in the following sectors: Healthcare, transportation, finance, water supply, waste management, energy, digital infrastructure, telecommunications, medical device and chemical manufacturing, food, aerospace, postal administration and public administration. The regulation defines ten minimum requirements with which all covered companies must comply. Essential and significant entities must comply with the same requirements. The distinction between the two types of companies is made only in terms of monitoring measures and sanctions. Read more about who NIS2 applies to in this blogpost.
While implementing cybersecurity standards such as ISO 27001/27002, SOC 2 and NIS CSF go a long way, it is not enough to comply with the regulation.

The NIS 2 directive requires security measures to be put in place to manage supply chain security. In addition, suppliers must ensure security in network and information systems acquisition and maintenance
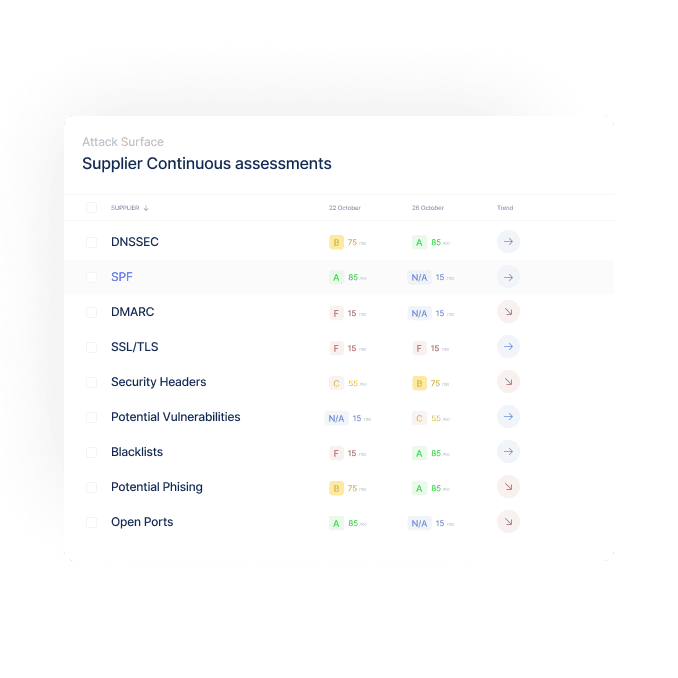
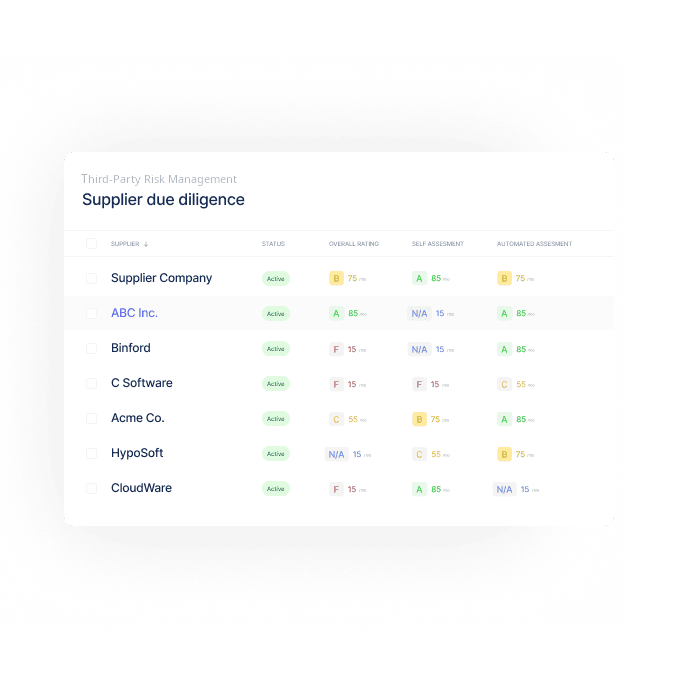
The Ceeyu SaaS platform enables businesses to assess and manage risks at suppliers using different techniques : digital questionnaires, data look up, and attack surface scans. Automated assessments in 10 different cybersecurity domains are performed on these assets to find and report vulnerabilities. Active vulnerability assessments and penetration tests can be carried out on request, in addition to the default passive vulnerability scans. This gives you a 360° overview of security risks in your suppliers security controls implemented, or their digital services. Thanks to the digital questionnaire module, you can survey your (potential) suppliers in any area of risk, such as financial health, regulatory compliance or ESG.
NIS2 underlines the importance of Third-Party Security Risk Management (TPsRM). From October 2024, all affected companies (estimated between 100,000 and 150,000), will have to periodically assess the quality of protection of their key suppliers' networks and information systems.
Ceeyu's SaaS platform can be used to scan not only your own network, but also that of your key suppliers. Because automated scans cannot cover all aspects of security, customers can also conduct assessments of their suppliers based on a library of standards-based questionnaire templates (ISO 27001, NIST, GDPR, etc.).
Our SaaS platform can alliviate your work with continous security risk identification of your network and IT systems and the ones of your critical suppliers.