4 min reading Mon Jun 27 2022
How to manage the third party risks posed by your critical suppliers
This blog post walks you through some ideas on how to navigate the complex web of third-party risks, focusing on critical suppliers.
First, we will briefly unpack each of the terms to get on the same line of thought. In doing this, there will be references to previous blog posts where we covered similar topics, in case you would like to dig deeper.
Third party risk management (TPRM) is the process by which organizations manage their suppliers. To keep things in perspective, for this article we distinguish between critical suppliers and non critical suppliers.
The focus is on critical suppliers because the relationship with a critical supplier or a critical vendor could have a substantial impact on the health and growth of a business.
What is a technology supply chain
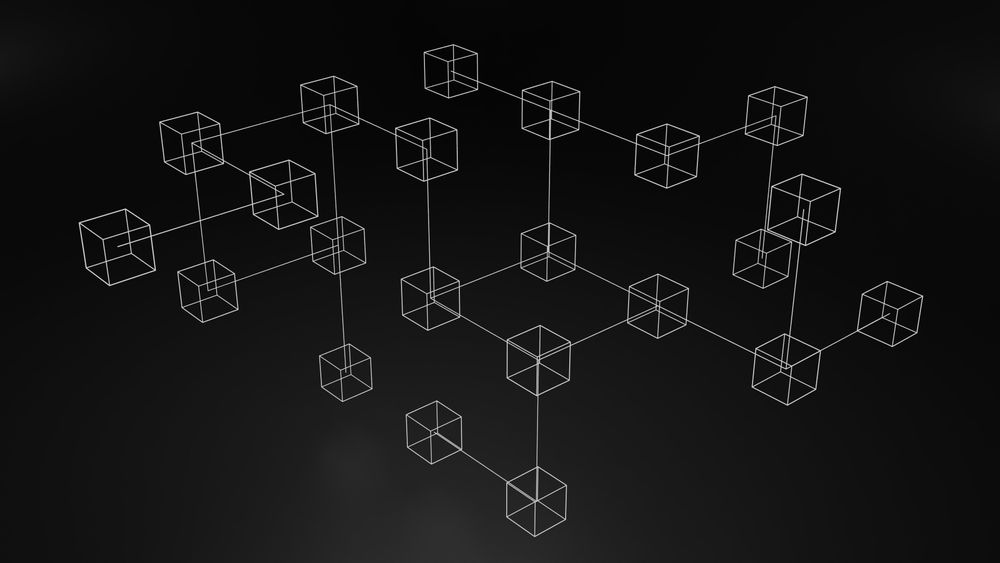
Let's consider a business that relies on IT suppliers to provide a service to its customers. At the level of IT and technology, all companies have at least one critical supplier. In reality, it is more likely that there is always a supply chain, which includes both critical suppliers and non-critical.
This IT-critical supplier could provide hardware, software, and networking equipment. At a deeper level, the supplier could be responsible for the maintenance and security of the operating system on employee computers and company servers. To make things more complex, the critical IT supplier could use IT services or software from another IT supplier. This is called a software supply chain, and the management of software supply chain risks is a topic in itself.
Coming back to the level of business, a critical supplier or critical vendor is core to business operation. On the one hand, this means that it is responsible for business-critical and potentially confidential data. On the other hand, it means that the critical vendor could be involved in every step of the service a business provides to its customers.
On this latter point, these are ways in which critical suppliers can be involved
- in ensuring the quality checks for the products and services
- in ensuring regulatory/ISO compliance, if the business operates in a highly regulated industry. This can mean providing a full audit assessment, review of risks and controls, and testing IT components and processes.
- providing the IT systems and technology supporting core business processes
- managing the relationship lifecycle with the customer or other third party partners - contract management, operational follow-up, or strategy adjustment
- ensuring the end-to-end operations for a critical business process
The list can go on. It is common for a critical supplier or critical vendor to fulfil multiple roles listed above. This can lead to a complexity that is hard to manage. For the purpose of this article, this is an IT supply chain.
What are the third party risks posed by critical suppliers
Now to get to the core of the matter, let's look at some issues that might arise when it comes to third-party risk
- Disruption of business continuity in case of unavailability of a critical supplier
- Reputational damage in case of a critical supplier suffering a data breach
- Financial impact resulting from changing suppliers last minute in case of an incident
- Fines resulting from a lack of due diligence on a low-maturity critical supplier
- Vendor lock-in or customer lock-in can make a business dependent on a vendor and unable to change vendors/suppliers without substantial costs
These are only some of the high-level risks which might arise regardless of the type of business or industry you are in. It is common for these risks to have ramifications depending on how deeply integrated into the core of the business a supplier or a vendor is.
In the next section, we will try to understand better how to deal with what is under the control of the business, and specifically how to manage risk once identified.
How to manage third party risks posed by critical suppliers
Once there is an assessment of the risk level for each vendor or supplier, it is important to prioritize risk. As a next step, we recommend defining a third party risk management program or an action plan to start mitigating the high risks.
Let's assume that we start with trying to mitigate business continuity disruption in case of unavailability of a critical supplier. A due diligence could materialize in a security questionnaire to be completed or even an on-site audit. Furthermore, the results can be used to propose a combination of continuous monitoring through a security rating system combined with a bi-yearly ad hoc self-assessment security questionnaire. This way, a business can ensure an accurate view of a high-risk vendor/supplier.
Risk management is key here; however, having a data back-up or a back-up plan for business continuity is just as important. This is especially important in case of a potential vendor lock-in, which can be one of the most problematic situations in which a business can find itself.
Similarly, a plan is needed in case of disaster recovery from a cybersecurity incident or other major business disruption.
Last but not least important, is reputation management in case of damage to the image or brand of the business, resulting from the negligence of a critical supplier. Having a prepared press release where the company takes accountability and reassures its customers or users will be essential to have if needed.
If you need help identifying your critical suppliers Ceeyu can support you take the first steps. Connect with us via [email protected]



